
The Wormhole hack demonstrated that the cryptocurrency industry is more vulnerable than most people think. According to blockchain analyst firm Chainalysis, more than $14 billion in crypto assets were stolen in 2021 alone.
One of the latest high-profile hacks to make the news was known as the Wormhole hack. The DeFi bridge platform had roughly $320 million stolen from its accounts in early February.
Cross-chain bridges may be uniquely susceptible to hacking attempts. But why is this the case, and how does it happen? In this post, we’ll go over the Wormhole hack and what you can do to protect your crypto.
Table of Contents
- What happened during the Wormhole hack?
- What is ‘Wormhole’?
- How did the Wormhole DeFi hack occur?
- What are the risks of using cross-chain bridges?
- Minimizing risks of bridge exploits with SecuX wallets
What happened during the Wormhole hack?
On February 2, 2022, the Wormhole platform was exploited for over $320 million. This event was the biggest hack in 2022. It was also the second-largest DeFi hack ever, behind the Poly Network hack in which another Ethereum bridge was attacked.
Following the attack, Wormhole stated that the vulnerability has been patched and that the platform will back fund one-for-one with Ethereum in the future. The funds were replaced by Wormhole’s parent company, Jump Crypto.
Wormhole developers Certus One offered a bug bounty program worth $10 million for the return of the stolen funds and an explanation of how it happened. This is one of the largest bug bounty programs in the crypto industry.
What is ‘Wormhole’?
Wormhole Network provides a communication bridge between blockchains. It allows different chains to transfer information and tokens seamlessly–at high speed and low cost.
The platform connects multiple blockchain networks, including Ethereum, Solana, Polygon, Terra, BNB Smart Chain, Oasis, and Avalanche.
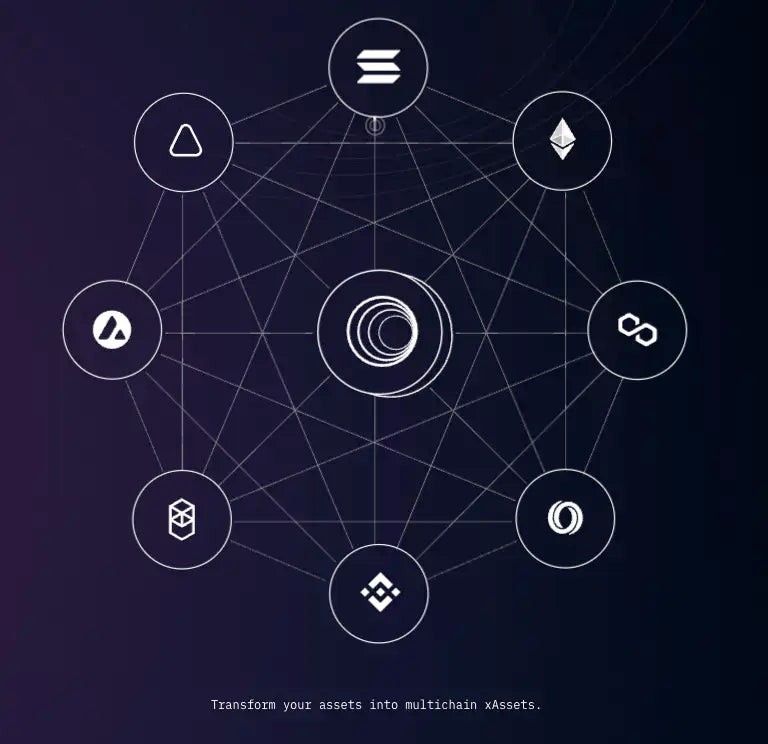
The Wormhole Network acts as a cross-chain integration system that allows some digital assets to move across various supported blockchains.
Using a bridge like Wormhole allows users to directly send or receive tokens between these networks.
By bypassing centralized exchanges, users can avoid tedious conversion processes and save money on transaction fees!
How did the Wormhole DeFi hack occur?
Before explaining how the hack occurred, let’s briefly go over how Wormhole allows users to move assets across blockchains.
Let’s say you want to move $ETH from Ethereum to Solana.
First, you lock up $ETH in Wormhole’s protocol and receive an equivalent amount of Solana-wrapped $ETH, known as $wETH. Essentially, the two assets become pegged, and 1 $ETH = 1 $wETH.
Due to a weakness in Wormhole’s code, the hacker freely minted 120,000 wrapped Ethereum ($wETH) on the Solana end of the bridge. However, instead of being binded by the 1:1 protocol peg, they were not forced to lock up any $ETH.
This, of course, meant that the newly-minted $wETH was not secured by the equivalent value of $ETH.
Then, the hacker moved at least 93,750 $wETH back across the bridge to the Ethereum blockchain, and used it to redeem actual $ETH.
The rest of the $wETH was converted to Solana’s native coin, $SOL.
What are the risks of cross-chain bridges?
People tend to think of blockchains as highly secure and unbreakable. While this is true in many cases, a growing number of high-profile hacks show that this isn’t always the case!
Theoretically, blockchain technology is incredibly secure. Bitcoin, for instance, has never suffered a successful attack on its main network.
However, that doesn’t mean cryptocurrency in broader terms is immune to hacks. New blockchains, decentralized applications, and DeFi platforms are being launched all the time. So, hackers choose to target projects with weaker security protocols and less industry experience.
DeFi is often targeted by hackers. At the time of writing, there have been an estimated 102 DeFi exploits resulting in losses of over $3.4 billion. Amongst all the types of various hacks to DeFi protocols, cross-chain bridges are particularly vulnerable.
Cross-chain bridges are built to move around tokens as quickly and cheaply as possible. So tokens are deposited by using internal representations of value, rather than moving the actual asset immediately.
While convenient, this sometimes allows hackers to withdraw tokens on one end of the bridge by utilizing its “line of credit.”
In comments posted to Reddit in January, Ethereum founder, Vitalik Buterin, highlighted the security limitations of cross-chain bridges.
He pointed out that 51% attacks on a bridge could compromise the value of tokens on that platform. As a result, he recommended that it’s always “safer to hold native assets” on their own blockchain instead of residing on compatible chains.
Buterin also suggested that this weakness could become a bigger problem as more chains become interconnected, stating, “If there are 100 chains, then there will end up being dapps with many interdependencies between those chains, and 51% attacking even one chain would create a systemic contagion that threatens the economy on that entire ecosystem.”
Minimizing risks of bridge exploits with SecuX wallets
The recent Wormhole hack has highlighted the risks associated with using dApps and smart contracts built on blockchain protocols. Despite the high level of security offered by blockchain technology itself, the code used in these applications can sometimes be flawed or contain bugs that leave your assets vulnerable to attack.
To protect yourself from these risks, it’s recommended to use a hardware wallet, also known as a cold wallet, to interact with dApps and smart contracts. By keeping your crypto stored offline, you can ensure that your assets remain safe and secure, even if the dApp or smart contract you’re using is compromised. Leaving your crypto stored on a decentralized exchange or other online platform can leave you exposed to bridge exploits and other security vulnerabilities.
If you want to ensure the safety of your digital assets, consider investing in a hardware wallet, which is a type of crypto wallet that provides enhanced security measures. With a hardware wallet, you can rest assured that your crypto is protected from potential hacks and cyberattacks. So, whether you’re a seasoned crypto investor or just getting started, be sure to use a hardware wallet to keep your assets secure.
We recommend our SecuX V20 for ultimate control over your crypto storage.
Our web application, SecuXess, connects to different blockchain networks. From here, you can safely perform transactions without ever recording your private information or needing to lock up your crypto on a decentralized finance exchange.
The app also allows users to send and receive crypto, connect with third-party services, and access smart contracts. For example, you can delegate voting rights on supported Proof of Stake blockchains.
Used in combination with the SecuX wallet, there is support for up to 500 accounts and over 1000 coins and tokens!
Your private keys remain offline and accessible only to you. Even if SecuX goes offline or gets shut down, you can still recover your crypto with your private seed phrase.
SecuX hardware wallets, in combination with SecuXess, are some of the most secure ways to interact with the vast world of cryptocurrency and blockchain protocols.
Before you trust your crypto with a DeFi platform like Wormhole’s cross-chain bridge, make sure you have a storage solution in place!
This way, you won’t need to hold your assets with a custodian for long. And remember, always do your own research.
0 comments